Unyt now supports configurable membranes — a joining workflow that lets network operators control who can participate in their network and under what conditions.
What's a membrane?
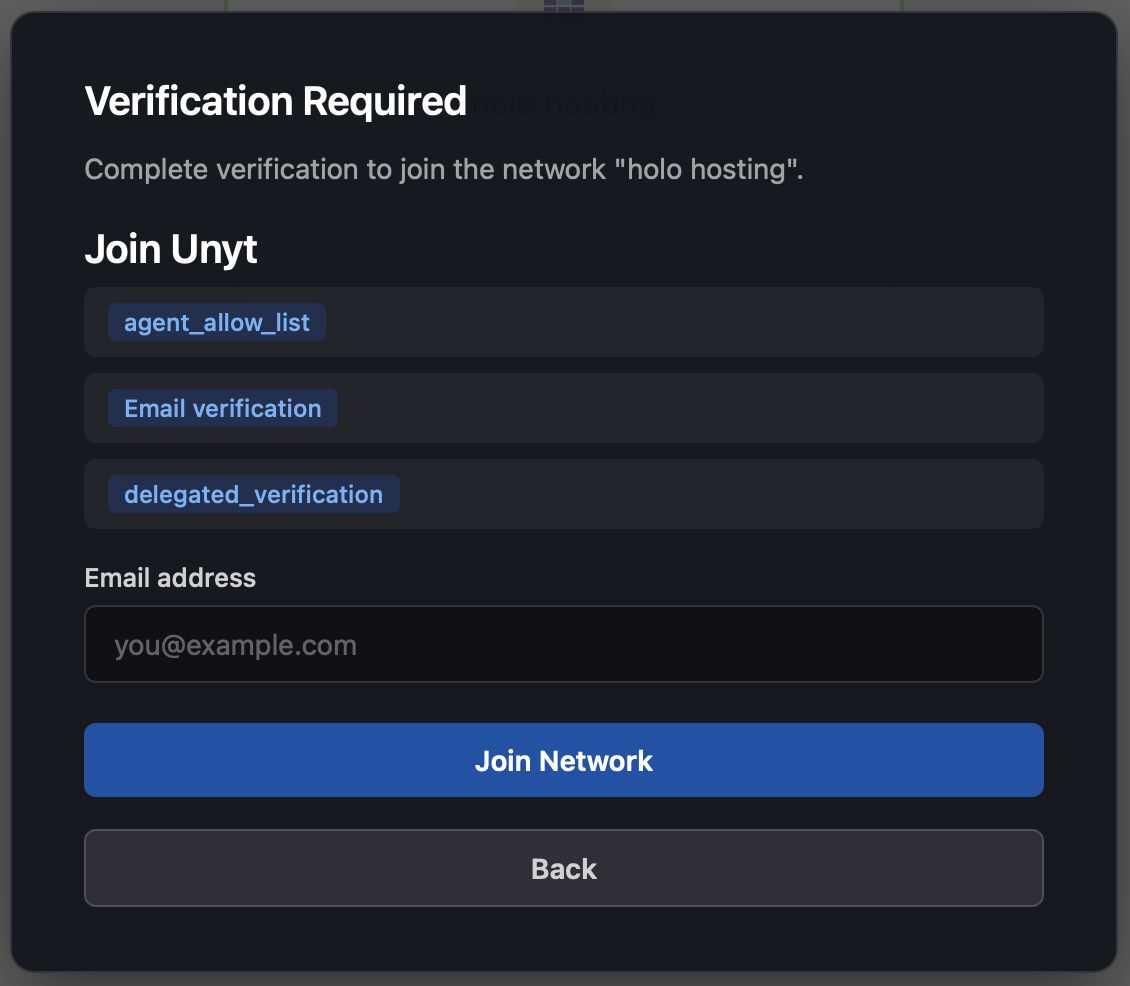
Holochain has always had membranes: cryptographic boundaries that determine who can join an app. Since the previous release of Unyt, we've worked with the Holochain team to add a layer on top of that — a joining process with configurable checkpoints. Each checkpoint presents a challenge that a prospective participant needs to complete before they can proceed. The challenges are modular. You can stack several together, use just one, or configure none at all — in which case users pass straight through with no friction.
Why would a community want one?
Different communities have different reasons for controlling who gets in. Here are the most common:
Sybil protection. A "Sybil attack" is when one person creates many fake identities to exploit a system. In a mutual-credit network like one built on Unyt, this can be a concern: if every new account gets a credit limit, someone spinning up fake accounts can run up debt across all of them and disappear. Similar risks apply to a system that distributes rewards, counts votes, or allocates resources per participant. Even a lightweight checkpoint — like verifying an email address — raises the cost of faking identities enough to deter abuse in many contexts.
Privacy and controlled access. Not every network is meant to be open. A neighborhood mutual-aid group, an internal company tool, or a private club each have good reasons to limit participation. This isn't necessarily about security — it's about context. Some spaces work better when the participants are known to each other or have been specifically invited.
Regulatory requirements. Some financial applications need to verify participant identity to meet KYC (Know Your Customer) or AML (Anti-Money Laundering) obligations. Modular membranes make it easy to satisfy those requirements for networks that need them, without imposing them on networks that don't.
Evolving needs. A network's requirements tend to change over time. You might start invite-only during a beta, open up with email verification at launch, and later add stronger checks for participants who want access to higher-value transactions. Membranes can be reconfigured as the community grows.
Available checkpoint types
These are the mechanisms that Unyt (and other Holochain applications) now can support. Each is optional and they can be combined:
Fully Open — No authentication or proofs required. Anyone can join. Suitable for public experiments, open forums, or low-stakes applications.
Invite-Gated — Participation requires a single-use or shared invite code. Useful for private betas, curated communities, or deliberate growth through personal referral.
Email-Verified — A code sent to an email address confirms the user controls it. A simple baseline that makes automated account creation just a bit harder.
Device/Agent Whitelisting — Pre-approved cryptographic agent keys sign a nonce to prove identity. Designed for internal enterprise tools, IoT networks, or machine-to-machine interactions where every authorized device is known in advance.
Operator Approval & KYC — A human operator or external KYC provider reviews and approves prospective participants. Intended for regulated financial applications or environments where verified identity is a requirement.
Putting it together
The goal here is straightforward: Unyt provides the accounting infrastructure, and now it also makes accessible tools to decide who gets to join each particular Unyt Accounting Alliance. Operators set up the mechanisms of protection that their particular application needs and are able to adjust them over time.
A Question Worth Exploring
What is a membrane that you can envision making use of and how might it help your community?
Get Started:



